TL;DR Threat Reports is an automated tool designed to help Threat Intelligence (CTI) Analysts process the overwhelming volume of daily cybersecurity news and vendor reports.
Inspired by the need for quick, actionable intelligence, this project uses AI Agents (powered by Google Gemini) to transform heavy, clutter-filled HTML reports into structured "tl;dr" briefings, complete with CTI tags, technical evidence, and visual mindmaps.
Cybersecurity analysts often have to review dozens of reports daily from various vendors. It is practically impossible to read them all in depth.
This tool allows an analyst to:
- Quickly summarize news and reports into a standardized format.
- Identify key evidence (IOCs, TTPs, Adversaries) without reading the whole text.
- Prioritize which reports are worth a complete, manual review.
- Connect the dots visually using auto-generated Mermaid mindmaps.
This project requires uv. Clone the repository and install dependencies:
git clone https://github.com/brunosergi/tldr-threat-reports
cd tldr-threat-reports
uv sync- API Key: Create a
.envfile based on.env_exampleand add yourGEMINI_API_KEY. - LLM Settings: Adjust the model, temperature, and Output Language (e.g., English, Brazilian Portuguese) in
src/tldr_threat_reports/config/llm.yaml.
In this initial version, the process is semi-manual to validate the intelligence pipeline:
- Source Preparation: Copy a report's HTML source (
Ctrl + U) tosrc/tldr_threat_reports/example/01_raw_report.html. - Cleaning:
uv run clean-html(Outputs a lightweight Markdown file). - AI Generation:
uv run ai-generation(Extracts intelligence and saves todata/db.json). - Build Bulletin:
uv run build-report(Generates a polisheddata/reports.md).
- v2 Orchestration: A single
main.pyentry point to run the entire pipeline at once. - Automated Scraping: Input a URL directly; the script will handle fetching and cleaning automatically.
- Flexible AI Support: Support for multiple providers (OpenAI, Anthropic, Ollama) and flexible model selection.
- Automated Test Suite: Implement
pytestusing theexample/files to ensure processing reliability. - Rich UX: Add logging, progress spinners, and AI state indicators.
- Intelligence Cache: Prevent re-processing the same report twice.
- RSS Feed Support: A function to convert
db.jsoninto XML for RSS Readers. - IOC Defanging: Automatically defang extracted indicators (IPs, URLs) to ensure safe report distribution.
- Enhanced CTI Models: Integration with more specialized Cyber Threat Intelligence models.
View JSON Database Output (db.json)
{
"headline": "🐉 Game of Emperor: Unveiling Earth Estries' Global Cyber Espionage Operations",
"summary": "### Executive Overview\n* **Threat Actor**: Earth Estries (aka Salt Typhoon, FamousSparrow, GhostEmperor, UNC2286), a sophisticated Chinese APT group.\n* **Primary Targets**: Critical sectors including telecommunications, government entities, technology, and NGOs across the US, Asia-Pacific, Middle East, and South Africa.\n* **Key Malware**: Deployment of advanced backdoors such as `GHOSTSPIDER`, `SNAPPYBEE` (Deed RAT), `MASOL RAT`, and the `DEMODEX` rootkit.\n* **Initial Access**: Exploitation of public-facing server vulnerabilities (Ivanti, Fortinet, Sophos, and Microsoft Exchange).\n* **Operational Strategy**: Use of complex C&C infrastructure, living-off-the-land binaries (LOLBINs) for lateral movement, and modular malware for long-term espionage.\n\n### Technical Analysis\n\n#### Initial Access and Vulnerability Exploitation\nEarth Estries aggressively targets public-facing servers by exploiting several N-day vulnerabilities to establish a foothold:\n\n| Vulnerability | Description |\n| :--- | :--- |\n| Ivanti Connect Secure (`CVE-2023-46805`, `CVE-2024-21887`) | Authentication bypass and RCE chain. |\n| Fortinet FortiClient EMS (`CVE-2023-48788`) | SQL Injection vulnerability. |\n| Sophos Firewall (`CVE-2022-3236`) | Code injection allowing remote code execution. |\n| ProxyLogon (`CVE-2021-26855`, `CVE-2021-26857`, `CVE-2021-26858`, `CVE-2021-27065`) | Microsoft Exchange RCE chain. |\n\n#### Malware Deep Dive: GHOSTSPIDER\n`GHOSTSPIDER` is a multi-modular backdoor designed for stealth and flexibility. It uses a custom protocol over TLS for C&C communication. The infection flow involves a stager installed via `regsvr32.exe`, which loads a login module in memory to collect system information.\n\n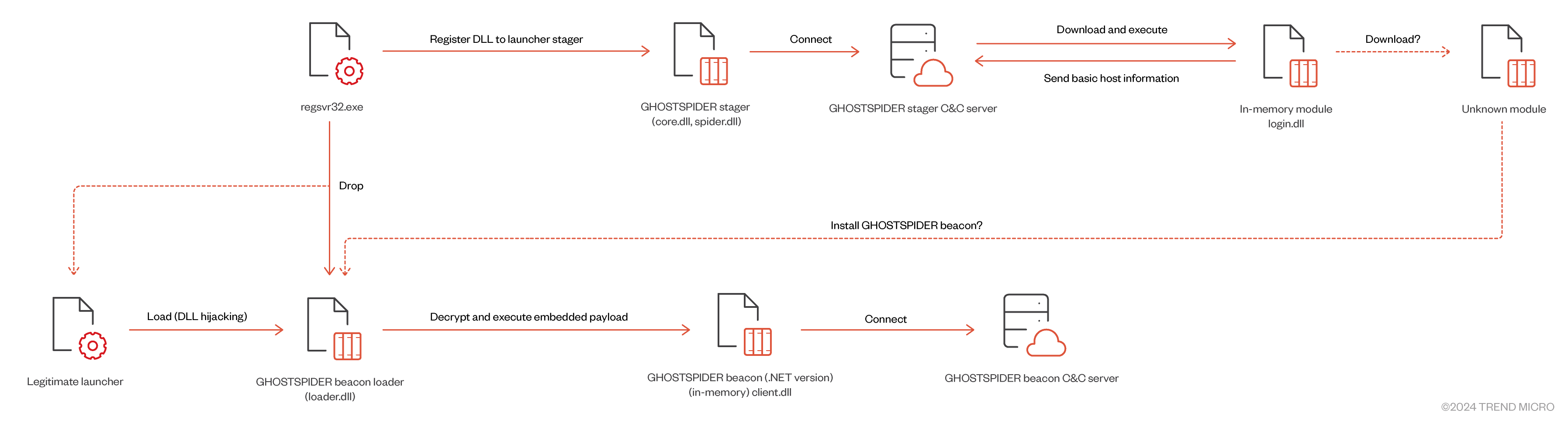\n\n**GHOSTSPIDER Beacon Command Codes:**\n\n| Code | Action | Description |\n| :--- | :--- | :--- |\n| 1 | upload | Load and invoke delegate from buffer. |\n| 2 | create | Call Open method from loaded delegate. |\n| 3 | normal | Call Write method from loaded delegate. |\n| 4 | close | Unload and remove the delegate. |\n| 5 | heartbeat | No action (keep-alive). |\n| 6 | update | Update idle time interval. |\n\n#### Persistence and Lateral Movement\nThe group utilizes the `DEMODEX` rootkit for long-term persistence. Recent variants use a CAB bundle to deploy payloads, making analysis difficult by deleting the bundle post-installation. For lateral movement, the group relies on LOLBINs:\n\n* `WMIC.exe`: Used for remote process creation.\n* `PSEXEC.exe`: Used for executing commands on remote hosts (e.g., `ps.exe /accepteula \\\\<TARGET> -u <USER> -p <PASS> -s cmd /c 1.bat`).\n* `frpc`: Fast Reverse Proxy for tunneling.\n\n#### Infrastructure and Attribution\nEarth Estries' operations show significant overlap with other Chinese APTs, suggesting shared toolsets from Malware-as-a-Service (MaaS) providers. \n\n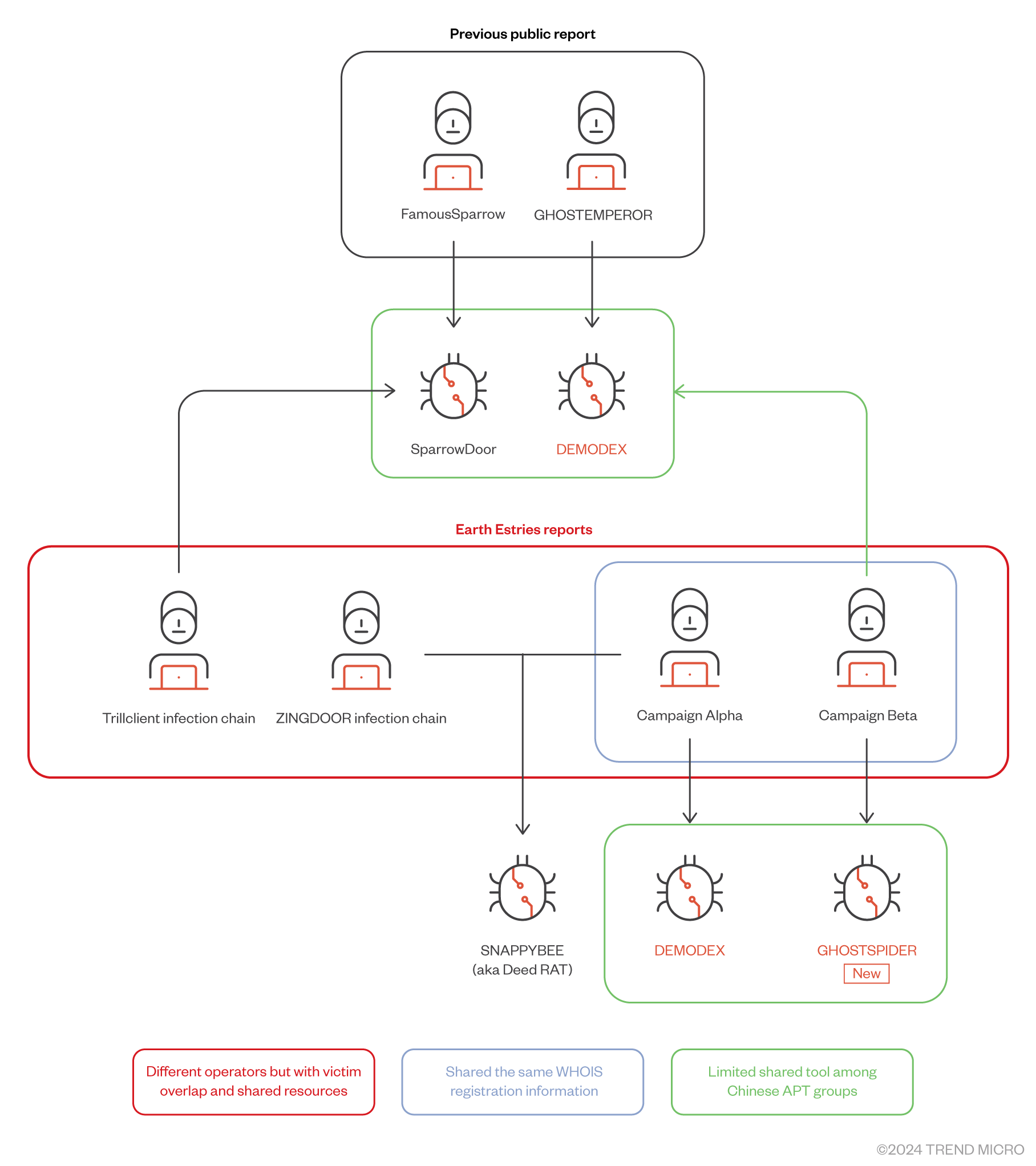\n\nVictim data exfiltrated from a US NGO included financial, HR, and business documents, as well as data related to military units and federal government entities.",
"severity": "CRITICAL",
"tags": {
"adversary": [
"Earth Estries",
"Salt Typhoon",
"FamousSparrow",
"GhostEmperor",
"UNC2286",
"UNC4841"
],
"victim": [
"US NGO",
"Taiwanese Government",
"Southeast Asian Telecommunications Companies"
],
"threat_type": [
"APT",
"Cyber Espionage",
"Rootkit",
"Malware"
],
"country": [
"USA",
"Taiwan",
"Vietnam",
"Thailand",
"Malaysia",
"Indonesia",
"Philippines",
"South Africa",
"Brazil",
"India",
"Pakistan",
"Afghanistan",
"Eswatini"
],
"industry": [
"Telecommunications",
"Government",
"Technology",
"Consulting",
"Chemical",
"Transportation",
"NGO"
],
"iocs": [
"23.81.41.166",
"165.154.227.192",
"103.91.64.214",
"158.247.222.165",
"103.159.133.251",
"api.solveblemten.com",
"esh.hoovernamosong.com",
"pulseathermakf.com",
"www.infraredsen.com",
"imap.dateupdata.com"
],
"cves": [
"CVE-2023-46805",
"CVE-2024-21887",
"CVE-2023-48788",
"CVE-2022-3236",
"CVE-2021-26855",
"CVE-2021-26857",
"CVE-2021-26858",
"CVE-2021-27065"
],
"mitre_ttps": [
"T1190",
"T1047",
"T1570",
"T1021.002",
"T1574.002",
"T1014",
"T1140",
"T1071.001"
]
},
"references": [
"https://www.trendmicro.com/en/research/23/h/earth-estries-targets-government-tech-for-cyberespionage.html",
"https://www.trendmicro.com/en/research/24/k/breaking-down-earth-estries-persistent-ttps-in-prolonged-cyber-o.html",
"https://learn.microsoft.com/en-us/defender-xdr/microsoft-threat-actor-naming",
"https://wsj.com/politics/national-security/u-s-officials-race-to-understand-severity-of-chinas-salt-typhoon-hacks-6e7c3951",
"https://global.ptsecurity.com/analytics/pt-esc-threat-intelligence/space-pirates-tools-and-connections",
"https://fortiguard.fortinet.com/jp/outbreak-alert/ivanti-authentication-bypass",
"https://gist.github.com/andrew-morris/7679a18ef815068897bf27bf631f2ede",
"https://securelist.com/ghostemperor-from-proxylogon-to-kernel-mode/104407/",
"https://cloud.google.com/blog/topics/threat-intelligence/unc4841-post-barracuda-zero-day-remediation",
"https://www.sygnia.co/blog/ghost-emperor-demodex-rootkit/",
"https://news.sophos.com/en-us/2022/10/19/covert-channels",
"https://www.reliaquest.com/blog/inc-ransom-attack-analysis-extortion-methodologies",
"https://rsvp.withgoogle.com/events/roocon24/sessions/session-11",
"https://www.welivesecurity.com/2021/09/23/famoussparrow-suspicious-hotel-guest/"
],
"mermaid": "mindmap\n root((Earth Estries Analysis))\n (🔍 Investigative Analysis)\n (Campaign Alpha)\n (Targeting Taiwan Gov and Chemical sector)\n (Open directory C&C 23.81.41.166)\n (Campaign Beta)\n (Long term Telecom and Gov targeting)\n (Discovery of GHOSTSPIDER backdoor)\n (Victimology)\n (Global reach US Asia Pacific Middle East South Africa)\n (Over 20 compromised organizations)\n (🎯 Attack Patterns)\n (Initial Access)\n (Exploiting Ivanti Fortinet Sophos Exchange)\n (Public facing server targeting)\n (Lateral Movement)\n (LOLBINs WMIC PSEXEC)\n (Customized malware deployment)\n (Persistence)\n (DEMODEX rootkit installation)\n (Registry based shellcode storage)\n (🛡 Defense Mechanisms)\n (Detection)\n (Trend Vision One platform)\n (YARA rules for malware families)\n (Hunting)\n (Queries for DEMODEX components)\n (IOC sweeping for C&C domains)\n (📊 Technical Evidence)\n (Malware Toolset)\n (GHOSTSPIDER modular backdoor)\n (SNAPPYBEE Deed RAT)\n (MASOL RAT Linux variant)\n (Infrastructure)\n (Shared C&C with ShadowPad and Cobalt Strike)\n (Use of SoftEther VPN for obfuscation)",
"timestamp": "2026-02-12T21:35:33.385599"
}View Rendered Bulletin (reports.md)
Generated on: 2026-02-12
- Adversary: Earth Estries, Salt Typhoon, FamousSparrow, GhostEmperor, UNC2286, UNC4841
- Victim: US NGO, Taiwanese Government, Southeast Asian Telecommunications Companies
- Threat Type: APT, Cyber Espionage, Rootkit, Malware
- Country: USA, Taiwan, Vietnam, Thailand, Malaysia, Indonesia, Philippines, South Africa, Brazil, India, Pakistan, Afghanistan, Eswatini
- Industry: Telecommunications, Government, Technology, Consulting, Chemical, Transportation, NGO
- IOCs: 23.81.41.166, 165.154.227.192, 103.91.64.214, 158.247.222.165, 103.159.133.251, api.solveblemten.com, esh.hoovernamosong.com, pulseathermakf.com, www.infraredsen.com, imap.dateupdata.com
- CVEs: CVE-2023-46805, CVE-2024-21887, CVE-2023-48788, CVE-2022-3236, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065
- Mitre TTPs: T1190, T1047, T1570, T1021.002, T1574.002, T1014, T1140, T1071.001
mindmap
root((Earth Estries Analysis))
(🔍 Investigative Analysis)
(Campaign Alpha)
(Targeting Taiwan Gov and Chemical sector)
(Open directory C&C 23.81.41.166)
(Campaign Beta)
(Long term Telecom and Gov targeting)
(Discovery of GHOSTSPIDER backdoor)
(Victimology)
(Global reach US Asia Pacific Middle East South Africa)
(Over 20 compromised organizations)
(🎯 Attack Patterns)
(Initial Access)
(Exploiting Ivanti Fortinet Sophos Exchange)
(Public facing server targeting)
(Lateral Movement)
(LOLBINs WMIC PSEXEC)
(Customized malware deployment)
(Persistence)
(DEMODEX rootkit installation)
(Registry based shellcode storage)
(🛡 Defense Mechanisms)
(Detection)
(Trend Vision One platform)
(YARA rules for malware families)
(Hunting)
(Queries for DEMODEX components)
(IOC sweeping for C&C domains)
(📊 Technical Evidence)
(Malware Toolset)
(GHOSTSPIDER modular backdoor)
(SNAPPYBEE Deed RAT)
(MASOL RAT Linux variant)
(Infrastructure)
(Shared C&C with ShadowPad and Cobalt Strike)
(Use of SoftEther VPN for obfuscation)
- Threat Actor: Earth Estries (aka Salt Typhoon, FamousSparrow, GhostEmperor, UNC2286), a sophisticated Chinese APT group.
- Primary Targets: Critical sectors including telecommunications, government entities, technology, and NGOs across the US, Asia-Pacific, Middle East, and South Africa.
- Key Malware: Deployment of advanced backdoors such as
GHOSTSPIDER,SNAPPYBEE(Deed RAT),MASOL RAT, and theDEMODEXrootkit. - Initial Access: Exploitation of public-facing server vulnerabilities (Ivanti, Fortinet, Sophos, and Microsoft Exchange).
- Operational Strategy: Use of complex C&C infrastructure, living-off-the-land binaries (LOLBINs) for lateral movement, and modular malware for long-term espionage.
Earth Estries aggressively targets public-facing servers by exploiting several N-day vulnerabilities to establish a foothold:
| Vulnerability | Description |
|---|---|
Ivanti Connect Secure (CVE-2023-46805, CVE-2024-21887) |
Authentication bypass and RCE chain. |
Fortinet FortiClient EMS (CVE-2023-48788) |
SQL Injection vulnerability. |
Sophos Firewall (CVE-2022-3236) |
Code injection allowing remote code execution. |
ProxyLogon (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065) |
Microsoft Exchange RCE chain. |
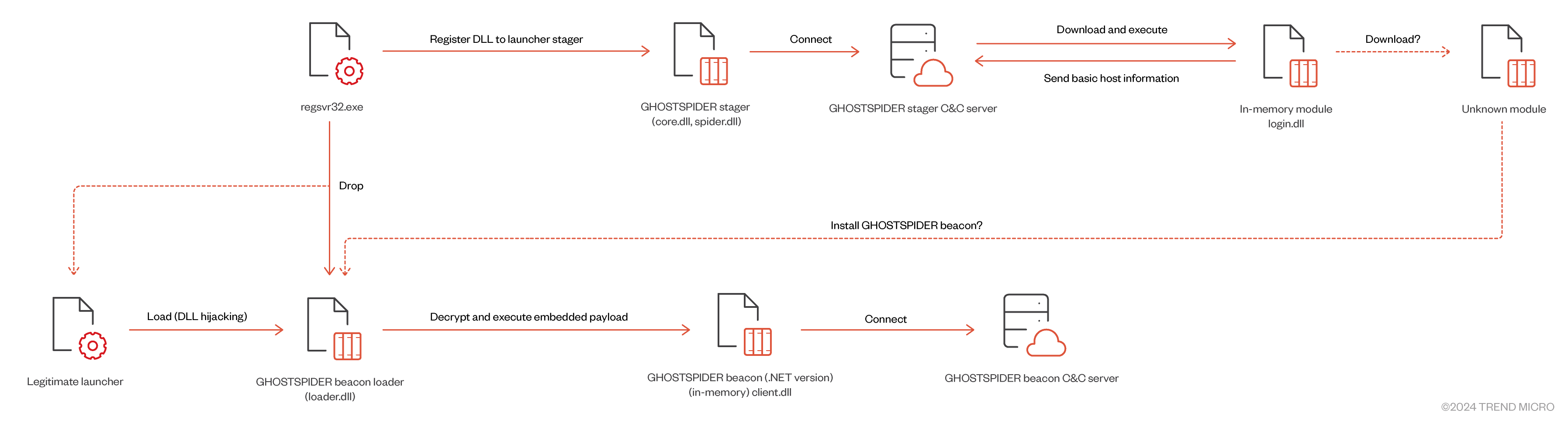
GHOSTSPIDER is a multi-modular backdoor designed for stealth and flexibility. It uses a custom protocol over TLS for C&C communication. The infection flow involves a stager installed via regsvr32.exe, which loads a login module in memory to collect system information.
GHOSTSPIDER Beacon Command Codes:
| Code | Action | Description |
|---|---|---|
| 1 | upload | Load and invoke delegate from buffer. |
| 2 | create | Call Open method from loaded delegate. |
| 3 | normal | Call Write method from loaded delegate. |
| 4 | close | Unload and remove the delegate. |
| 5 | heartbeat | No action (keep-alive). |
| 6 | update | Update idle time interval. |
The group utilizes the DEMODEX rootkit for long-term persistence. Recent variants use a CAB bundle to deploy payloads, making analysis difficult by deleting the bundle post-installation. For lateral movement, the group relies on LOLBINs:
WMIC.exe: Used for remote process creation.PSEXEC.exe: Used for executing commands on remote hosts (e.g.,ps.exe /accepteula \\<TARGET> -u <USER> -p <PASS> -s cmd /c 1.bat).frpc: Fast Reverse Proxy for tunneling.
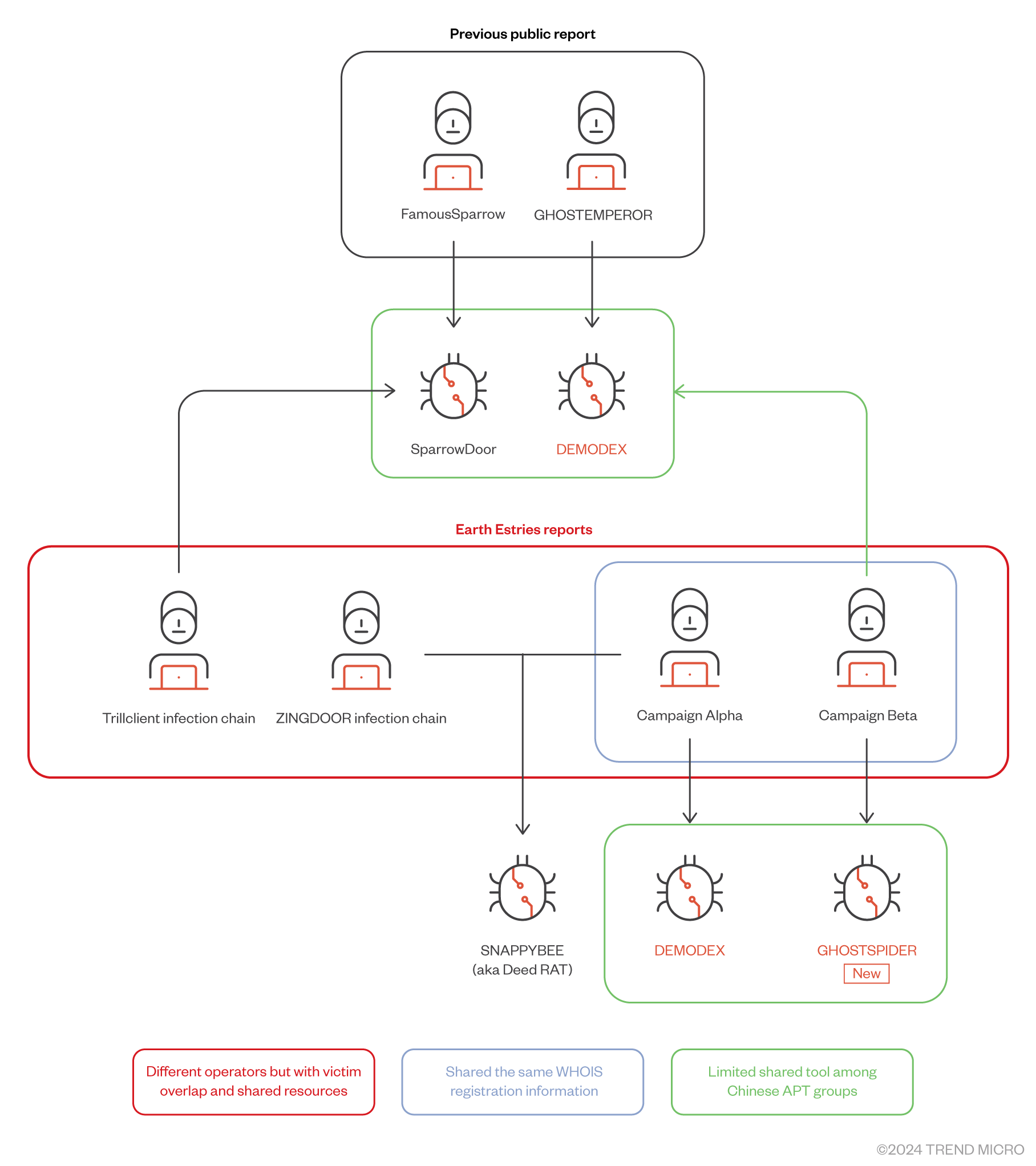
Earth Estries' operations show significant overlap with other Chinese APTs, suggesting shared toolsets from Malware-as-a-Service (MaaS) providers.
Victim data exfiltrated from a US NGO included financial, HR, and business documents, as well as data related to military units and federal government entities.
- https://www.trendmicro.com/en/research/23/h/earth-estries-targets-government-tech-for-cyberespionage.html
- https://www.trendmicro.com/en/research/24/k/breaking-down-earth-estries-persistent-ttps-in-prolonged-cyber-o.html
- https://learn.microsoft.com/en-us/defender-xdr/microsoft-threat-actor-naming
- https://wsj.com/politics/national-security/u-s-officials-race-to-understand-severity-of-chinas-salt-typhoon-hacks-6e7c3951
- https://global.ptsecurity.com/analytics/pt-esc-threat-intelligence/space-pirates-tools-and-connections
- https://fortiguard.fortinet.com/jp/outbreak-alert/ivanti-authentication-bypass
- https://gist.github.com/andrew-morris/7679a18ef815068897bf27bf631f2ede
- https://securelist.com/ghostemperor-from-proxylogon-to-kernel-mode/104407/
- https://cloud.google.com/blog/topics/threat-intelligence/unc4841-post-barracuda-zero-day-remediation
- https://www.sygnia.co/blog/ghost-emperor-demodex-rootkit/
- https://news.sophos.com/en-us/2022/10/19/covert-channels
- https://www.reliaquest.com/blog/inc-ransom-attack-analysis-extortion-methodologies
- https://rsvp.withgoogle.com/events/roocon24/sessions/session-11
- https://www.welivesecurity.com/2021/09/23/famoussparrow-suspicious-hotel-guest/
👉 View full generated reports here
⭐ Star this repo if you find it useful!